Stay up to date the most pressing cyber threats, emerging trends and what they mean for enterprise security, critical infrastructure and global risk.
Executive Summary
The week of August 23-29, 2025 was characterized by systematic exploitation of critical infrastructure vulnerabilities by Chinese and Russian nation-state actors, combined with multiple zero-day vulnerabilities under active exploitation across enterprise platforms. CISA and 22 international partners released joint advisory AA25-239A detailing Chinese APT operations compromising over 600 organizations globally through systematic exploitation of six high-severity vulnerabilities in Cisco, Ivanti, and Palo Alto Networks equipment. Concurrently, Russian APT group Static Tundra continues exploiting Cisco Smart Install vulnerabilities to deploy SYNful Knock firmware implants against Ukrainian and allied critical infrastructure.
Four zero-day vulnerabilities confirmed under active exploitation include CVE-2025-7775 (Citrix NetScaler, CVSS 9.4), CVE-2025-57819 (FreePBX, CVSS 10.0), CVE-2025-8088 (WinRAR exploited by RomCom), and CVE-2025-43300 (Apple Image I/O).,,, Microsoft's August Patch Tuesday addressed 107 vulnerabilities including publicly disclosed Kerberos zero-day CVE-2025-53779. Systematic targeting of cloud CRM platforms demonstrates coordinated campaign against Salesforce implementations, with confirmed breaches at TransUnion (4.4M records), pharmaceutical companies through Qilin ransomware, and multiple technology firms.,,,
Analyst Comment: The convergence of nation-state infrastructure targeting with widespread zero-day exploitation across multiple platforms indicates coordinated escalation requiring immediate cross-sector defensive response and comprehensive infrastructure security review.
Critical Incidents
1. Chinese APT Multi-CVE Infrastructure Exploitation Campaign
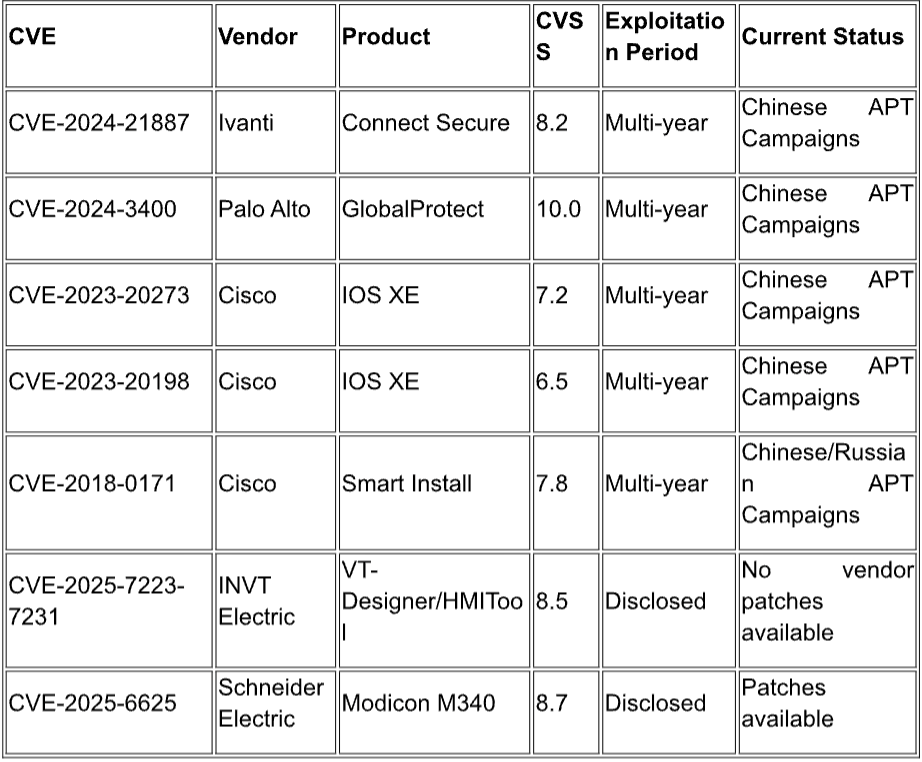
Chinese state-sponsored actors systematically exploit six high-severity vulnerabilities to maintain persistent access to global critical infrastructure: CVE-2024-21887 (Ivanti Connect Secure), CVE-2024-3400 (Palo Alto GlobalProtect), CVE-2023-20273 and CVE-2023-20198 (Cisco IOS XE), and CVE-2018-0171 (Cisco Smart Install). Operations overlap with Salt Typhoon, OPERATOR PANDA, RedMike, UNC5807, and GhostEmperor campaigns, compromising over 600 organizations across 80+ countries with focus on telecommunications backbone infrastructure. Threat actors modify router configurations to establish GRE tunnels for persistent access and harvest TACACS+ traffic for network administrator credential theft.
Analyst Comment: Multi-year exploitation of critical infrastructure vulnerabilities spanning 2018-2024 indicates systematic failure in network device lifecycle management requiring immediate comprehensive infrastructure security audit.
2. Citrix NetScaler Zero-Day Mass Exploitation (CVE-2025-7775)
CISA added CVE-2025-7775 to the Known Exploited Vulnerabilities catalog on August 26, 2025, following vendor confirmation of active exploitation against unmitigated Citrix NetScaler ADC and Gateway appliances. The memory overflow vulnerability enables pre-authentication remote code execution and denial of service with CVSS score 9.4, affecting approximately 28,200 internet-exposed instances globally. Federal agencies face August 28, 2025 patching deadline, with security researchers reporting only 16% patch adoption as of August 27.
Analyst Comment: The combination of maximum severity, confirmed exploitation, and low patch adoption creates immediate risk for persistent VPN infrastructure compromise across critical sectors.
3. WinRAR Zero-Day Campaign by RomCom (CVE-2025-8088)
RomCom threat group actively exploits CVE-2025-8088, a directory-traversal vulnerability in WinRAR, targeting financial, manufacturing, defense, and logistics firms through spear-phishing emails with malicious RAR attachments disguised as job applications. The vulnerability affects widespread WinRAR installations globally, with patches available in version 7.13 requiring manual updates. Attack methodology demonstrates sophisticated social engineering combined with zero-day exploitation for initial access to high-value networks.
Analyst Comment: RomCom's systematic targeting of critical infrastructure sectors using zero-day exploitation requires immediate WinRAR updates and enhanced email security controls for job application processing workflows.
4. FreePBX Maximum Severity Zero-Day (CVE-2025-57819)
Sangoma FreePBX Security Team disclosed active exploitation of CVE-2025-57819, a CVSS 10.0 vulnerability affecting FreePBX systems with Administrator Control Panel exposed to the internet, with attacks observed since August 21, 2025. The vulnerability enables unauthenticated access leading to arbitrary database manipulation and remote code execution, with documented compromise of 3,000 SIP extensions and 500 trunks at a single organization. Security researchers warn of active backdoor deployment with potential for ransomware operations and telecommunications fraud.
Analyst Comment: Maximum severity zero-day exploitation of telecommunications infrastructure requires immediate security review of all VoIP systems for unauthorized access and fraudulent activity indicators.
Active Threat Actors
Static Tundra (Russian APT)
Russian-affiliated APT group Static Tundra actively exploits CVE-2018-0171 in Cisco IOS Smart Install to target unpatched and end-of-life network devices globally, with primary focus on Ukraine and allied nations' critical infrastructure. The group employs SYNful Knock firmware implants for persistent access, demonstrating sophisticated understanding of networking infrastructure for long-term espionage operations. Campaign targets include telecommunications backbone systems, government networks, and critical infrastructure across energy and transportation sectors with emphasis on disrupting Ukrainian operations.
RomCom (Advanced Cybercriminal Group)
RomCom demonstrates advanced capabilities through systematic exploitation of WinRAR CVE-2025-8088 zero-day vulnerability, targeting financial, manufacturing, defense, and logistics firms through sophisticated spear-phishing campaigns. The group uses malicious RAR attachments disguised as legitimate job applications to deliver initial compromise, followed by systematic network reconnaissance and data exfiltration. Operations indicate coordination with broader cybercriminal ecosystem and potential nation-state connections based on targeting patterns and technical sophistication levels.
ShinyHunters Collective (Salesforce Supply Chain Campaign)
ShinyHunters systematically targets cloud-based CRM platforms through coordinated social engineering campaigns, compromising Salesforce implementations at TransUnion (4.4M records), pharmaceutical companies, and technology firms. The group employs voice phishing techniques impersonating HR/IT personnel to obtain OAuth application approvals, enabling large-scale data exfiltration operations. Attack methodology includes business contact information harvesting for downstream targeting and supply chain compromise affecting customer organizations.
Qilin Ransomware Group
Qilin ransomware group continues targeting healthcare and pharmaceutical sectors, with confirmed compromise of Inotiv pharmaceutical company resulting in theft of approximately 162,000 files totaling 176GB of sensitive data. The attack demonstrates continued evolution of double-extortion ransomware operations with focus on high-value healthcare data for maximum leverage in extortion negotiations. Operations indicate broader surge in healthcare sector targeting across multiple ransomware groups during the collection period.
Trends
Nation-State Infrastructure Persistence Operations
Chinese and Russian APT groups demonstrate systematic approaches to maintaining long-term access to critical infrastructure through exploitation of network device vulnerabilities spanning multiple years. Chinese APT operations exploit six distinct CVEs ranging from 2018-2024, while Russian Static Tundra continues leveraging CVE-2018-0171 from 2018., Both campaigns focus on telecommunications backbone infrastructure and government networks, using firmware modification and configuration changes to establish persistent access independent of traditional endpoint security controls. Intelligence reveals over 600 organizations compromised by Chinese actors alone, with Russian operations concentrated on Ukrainian and allied infrastructure.
Analyst Comment: Multi-year exploitation of network infrastructure vulnerabilities indicates systematic failure to address critical device patching and lifecycle management, requiring comprehensive audit of network infrastructure security posture.
Zero-Day Exploitation Acceleration Across Critical Platforms
August 2025 demonstrates accelerated zero-day exploitation activity, with four maximum severity vulnerabilities under active exploitation: CVE-2025-7775 (Citrix NetScaler, CVSS 9.4), CVE-2025-57819 (FreePBX, CVSS 10.0), CVE-2025-8088 (WinRAR), and CVE-2025-43300 (Apple Image I/O).,,, Apple's patch represents the seventh actively exploited zero-day addressed in 2025, while Microsoft's August Patch Tuesday addressed 107 vulnerabilities including publicly disclosed Kerberos zero-day CVE-2025-53779., CISA added four vulnerabilities to the Known Exploited Vulnerabilities catalog during the collection period, including CVE-2025-48384 (Git) and two Citrix Session Recording vulnerabilities.,
Analyst Comment: The sustained zero-day exploitation rate across multiple platforms indicates threat actors maintain advanced vulnerability research capabilities that consistently outpace defensive patching cycles, requiring enhanced zero-day detection and emergency response procedures.
Systematic Cloud CRM Platform Supply Chain Attacks
Intelligence reveals coordinated targeting of cloud-based customer relationship management platforms, with systematic Salesforce exploitation campaigns affecting over 8.9 million records across multiple organizations during August 20250.,, Attack methodology involves sophisticated voice phishing campaigns impersonating HR/IT personnel to obtain OAuth application approvals, enabling systematic data exfiltration from customer support systems. Confirmed targeting includes TransUnion credit reporting (4.4M records), pharmaceutical sector companies, and technology firms, suggesting shared infrastructure and techniques among threat actors focused on CRM supply chain compromise.,
Analyst Comment: Systematic CRM platform targeting represents evolution toward supply chain attacks against business-critical cloud services, requiring enhanced OAuth application monitoring and verification procedures for high-privilege cloud platform access requests.
Vulnerabilities
Critical Patches Required This Month
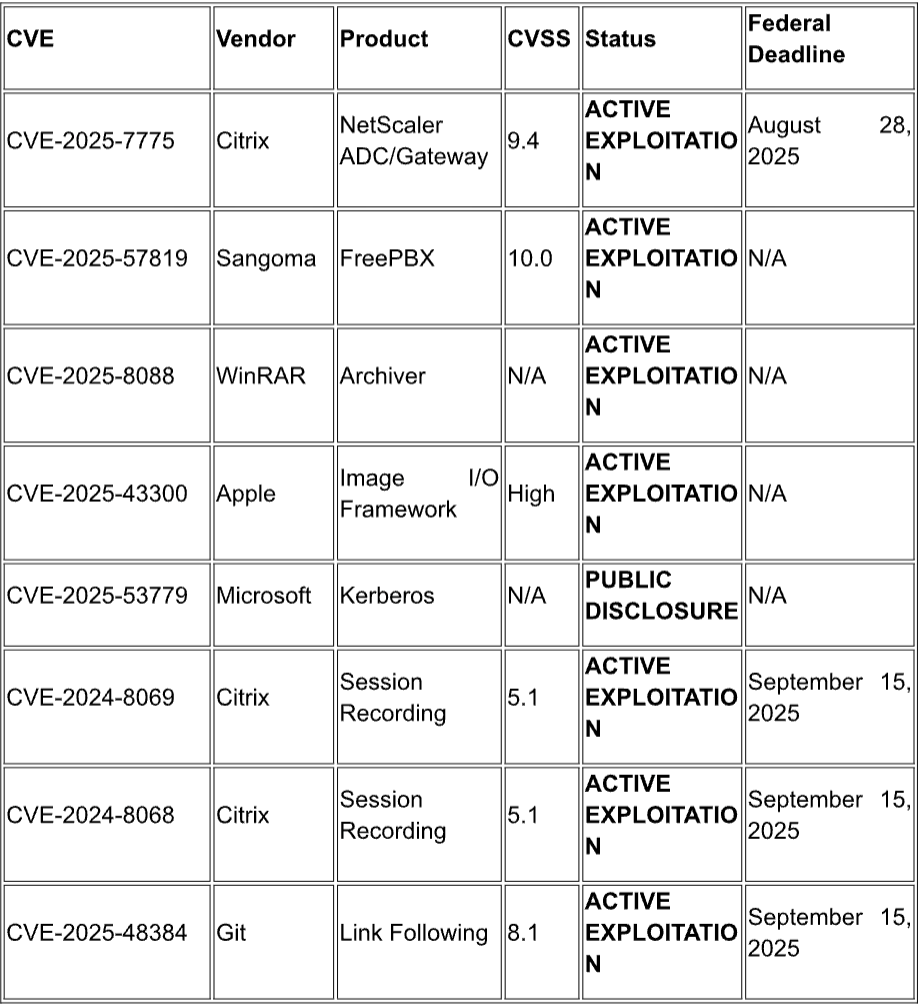
Continuing Active Exploitation
Recommendations
Immediate Actions (0-24 Hours)
- Deploy emergency patches for CVE-2025-7775 (Citrix NetScaler), CVE-2025-57819 (FreePBX), and CVE-2025-8088 (WinRAR) and conduct comprehensive incident response on all affected systems for indicators of compromise
- Update all Apple devices to iOS 18.6.2, iPadOS 18.6.2, macOS Sequoia 15.6.1, Sonoma 14.7.8, and Ventura 13.7.8 to address CVE-2025-43300 zero-day exploitation
- Immediately patch all Chinese and Russian APT-exploited CVEs in network infrastructure: CVE-2024-21887, CVE-2024-3400, CVE-2023-20273, CVE-2023-20198, and CVE-2018-0171
- Block public access to FreePBX Administrator Control Panel interfaces and conduct security assessment of all VoIP systems for unauthorized access, fraudulent call patterns, and credential compromise indicators
- Cybersecurity and Infrastructure Security Agency. (2025, August 27). Countering Chinese State-Sponsored Actors Compromise of Networks Worldwide to Feed Global Espionage System. CISA. https://www.cisa.gov/news-events/cybersecurity-advisories/aa25-239a
- Check Point Research. (2025, August 18-24). Weekly intelligence report: August 18-24, 2025. Check Point Research.
- Cybersecurity and Infrastructure Security Agency. (2025, August 26). CISA adds one known exploited vulnerability to catalog. CISA. https://www.cisa.gov/news-events/alerts/2025/08/26/cisa-adds-one-known-exploited-vulnerability-catalog
- The Hacker News. (2025, August 28). FreePBX servers targeted by zero-day flaw, emergency patch now available. https://thehackernews.com/2025/08/freepbx-servers-targeted-by-zero-day.html
- Tata Communications. (2025, August 26). Your weekly threat intelligence advisory. Tata Communications Threat Intelligence.
- Paganini, P. (2025, August 29). Apple addressed the seventh actively exploited zero-day. Security Affairs. https://securityaffairs.com/181394/security/apple-addressed-the-seventh-actively-exploited-zero-day.html
- CrowdStrike. (2025, August 13). August 2025 Patch Tuesday: Updates and analysis. https://www.crowdstrike.com/en-us/blog/patch-tuesday-analysis-august-2025/
- Toulas, B. (2025, August 28). TransUnion suffers data breach impacting over 4.4 million people. BleepingComputer. https://www.bleepingcomputer.com/news/security/transunion-suffers-data-breach-impacting-over-44-million-people/
- Trend Micro News. (2025, August 26). Google data breach exposes 2.5 billion Gmail users to new scam risks. https://news.trendmicro.com/2025/08/26/google-data-breach-gmail/
- Trend Micro News. (2025, August 26). Google data breach exposes 2.5 billion Gmail users to new scam risks.
- FireCompass. (2025, August 25). Farmers insurance data breach: Over 1.1 million customers affected in sophisticated cloud attack. FireCompass. https://firecompass.com/farmers-insurance-data-breach-over-1-1-million-customers-affected-in-sophisticated-cloud-attack/
- Cybersecurity and Infrastructure Security Agency. (2025, August 27). Countering Chinese State-Sponsored Actors Compromise of Networks Worldwide to Feed Global Espionage System. CISA. https://www.cisa.gov/news-events/cybersecurity-advisories/aa25-239a
- Cybersecurity and Infrastructure Security Agency. (2025, August 27). Countering Chinese State-Sponsored Actors Compromise of Networks Worldwide to Feed Global Espionage System. CISA. https://www.cisa.gov/news-events/cybersecurity-advisories/aa25-239a
- Cybersecurity and Infrastructure Security Agency. (2025, August 27). Countering Chinese State-Sponsored Actors Compromise of Networks Worldwide to Feed Global Espionage System. CISA. https://www.cisa.gov/news-events/cybersecurity-advisories/aa25-239a
- Cybersecurity and Infrastructure Security Agency. (2025, August 26). CISA adds one known exploited vulnerability to catalog. CISA. https://www.cisa.gov/news-events/alerts/2025/08/26/cisa-adds-one-known-exploited-vulnerability-catalog
- Cybersecurity and Infrastructure Security Agency. (2025, August 26). CISA adds one known exploited vulnerability to catalog. CISA. https://www.cisa.gov/news-events/alerts/2025/08/26/cisa-adds-one-known-exploited-vulnerability-catalog
- Cybersecurity and Infrastructure Security Agency. (2025, August 26). CISA adds one known exploited vulnerability to catalog. CISA. https://www.cisa.gov/news-events/alerts/2025/08/26/cisa-adds-one-known-exploited-vulnerability-catalog
- Tata Communications. (2025, August 26). Your weekly threat intelligence advisory. Tata Communications Threat Intelligence.
- Tata Communications. (2025, August 26). Your weekly threat intelligence advisory. Tata Communications Threat Intelligence.
- The Hacker News. (2025, August 28). FreePBX servers targeted by zero-day flaw, emergency patch now available. https://thehackernews.com/2025/08/freepbx-servers-targeted-by-zero-day.html
- The Hacker News. (2025, August 28). FreePBX servers targeted by zero-day flaw, emergency patch now available. https://thehackernews.com/2025/08/freepbx-servers-targeted-by-zero-day.html
- The Hacker News. (2025, August 28). FreePBX servers targeted by zero-day flaw, emergency patch now available. https://thehackernews.com/2025/08/freepbx-servers-targeted-by-zero-day.html
- Check Point Research. (2025, August 18-24). Weekly intelligence report: August 18-24, 2025. Check Point Research.
- Check Point Research. (2025, August 18-24). Weekly intelligence report: August 18-24, 2025. Check Point Research.
- Check Point Research. (2025, August 18-24). Weekly intelligence report: August 18-24, 2025. Check Point Research.
- Tata Communications. (2025, August 26). Your weekly threat intelligence advisory. Tata Communications Threat Intelligence.
- Tata Communications. (2025, August 26). Your weekly threat intelligence advisory. Tata Communications Threat Intelligence.
- Tata Communications. (2025, August 26). Your weekly threat intelligence advisory. Tata Communications Threat Intelligence.
- Trend Micro News. (2025, August 26). Google data breach exposes 2.5 billion Gmail users to new scam risks. https://news.trendmicro.com/2025/08/26/google-data-breach-gmail/
- FireCompass. (2025, August 25). Farmers insurance data breach: Over 1.1 million customers affected in sophisticated cloud attack. FireCompass. https://firecompass.com/farmers-insurance-data-breach-over-1-1-million-customers-affected-in-sophisticated-cloud-attack/
- FireCompass. (2025, August 25). Farmers insurance data breach: Over 1.1 million customers affected in sophisticated cloud attack. FireCompass. https://firecompass.com/farmers-insurance-data-breach-over-1-1-million-customers-affected-in-sophisticated-cloud-attack/
- FireCompass. (2025, August 25). Farmers insurance data breach: Over 1.1 million customers affected in sophisticated cloud attack. FireCompass. https://firecompass.com/farmers-insurance-data-breach-over-1-1-million-customers-affected-in-sophisticated-cloud-attack/
- Cybersecurity and Infrastructure Security Agency. (2025, August 27). Countering Chinese State-Sponsored Actors Compromise of Networks Worldwide to Feed Global Espionage System. CISA. https://www.cisa.gov/news-events/cybersecurity-advisories/aa25-239a
- Check Point Research. (2025, August 18-24). Weekly intelligence report: August 18-24, 2025. Check Point Research.
- Check Point Research. (2025, August 18-24). Weekly intelligence report: August 18-24, 2025. Check Point Research.
- Tata Communications. (2025, August 26). Your weekly threat intelligence advisory. Tata Communications Threat Intelligence.
- The Hacker News. (2025, August 28). FreePBX servers targeted by zero-day flaw, emergency patch now available. https://thehackernews.com/2025/08/freepbx-servers-targeted-by-zero-day.html
- Tata Communications. (2025, August 26). Your weekly threat intelligence advisory. Tata Communications Threat Intelligence.
- Paganini, P. (2025, August 29). Apple addressed the seventh actively exploited zero-day. Security Affairs. https://securityaffairs.com/181394/security/apple-addressed-the-seventh-actively-exploited-zero-day.html
- Paganini, P. (2025, August 29). Apple addressed the seventh actively exploited zero-day. Security Affairs. https://securityaffairs.com/181394/security/apple-addressed-the-seventh-actively-exploited-zero-day.html
- CrowdStrike. (2025, August 13). August 2025 Patch Tuesday: Updates and analysis. https://www.crowdstrike.com/en-us/blog/patch-tuesday-analysis-august-2025/
- Cybersecurity and Infrastructure Security Agency. (2025, August 26). CISA adds one known exploited vulnerability to catalog. CISA. https://www.cisa.gov/news-events/alerts/2025/08/26/cisa-adds-one-known-exploited-vulnerability-catalog
- Cybersecurity and Infrastructure Security Agency. (2025, August 25). CISA adds three known exploited vulnerabilities to catalog. CISA. https://www.cisa.gov/news-events/alerts/2025/08/25/cisa-adds-three-known-exploited-vulnerabilities-catalog
- Toulas, B. (2025, August 28). TransUnion suffers data breach impacting over 4.4 million people. BleepingComputer. https://www.bleepingcomputer.com/news/security/transunion-suffers-data-breach-impacting-over-44-million-people/
- Trend Micro News. (2025, August 26). Google data breach exposes 2.5 billion Gmail users to new scam risks. https://news.trendmicro.com/2025/08/26/google-data-breach-gmail/=
- FireCompass. (2025, August 25). Farmers insurance data breach: Over 1.1 million customers affected in sophisticated cloud attack. FireCompass. https://firecompass.com/farmers-insurance-data-breach-over-1-1-million-customers-affected-in-sophisticated-cloud-attack/
- Toulas, B. (2025, August 28). TransUnion suffers data breach impacting over 4.4 million people. BleepingComputer. https://www.bleepingcomputer.com/news/security/transunion-suffers-data-breach-impacting-over-44-million-people/
- Trend Micro News. (2025, August 26). Google data breach exposes 2.5 billion Gmail users to new scam risks. https://news.trendmicro.com/2025/08/26/google-data-breach-gmail/


