In today's "perimeter-less" and web-first world, the browser has become the essential application across the workforce — even though it's also CISOs' most significant liability. Relying on standard browsers leaves administrators blind and the organization exposed as users access cloud apps or visit untrusted websites for work or personal browsing.
Silo is a secure enterprise browser used by IT teams to isolate all web-based activity — application access, personal browsing, web and email link opens — from ransomware, data exfiltration and phishing exploits in a cloud-based browsing environment.
Fully isolate devices from the web, eliminating your primary attack surface.
Zero need to install client software or an agent on end-user devices.
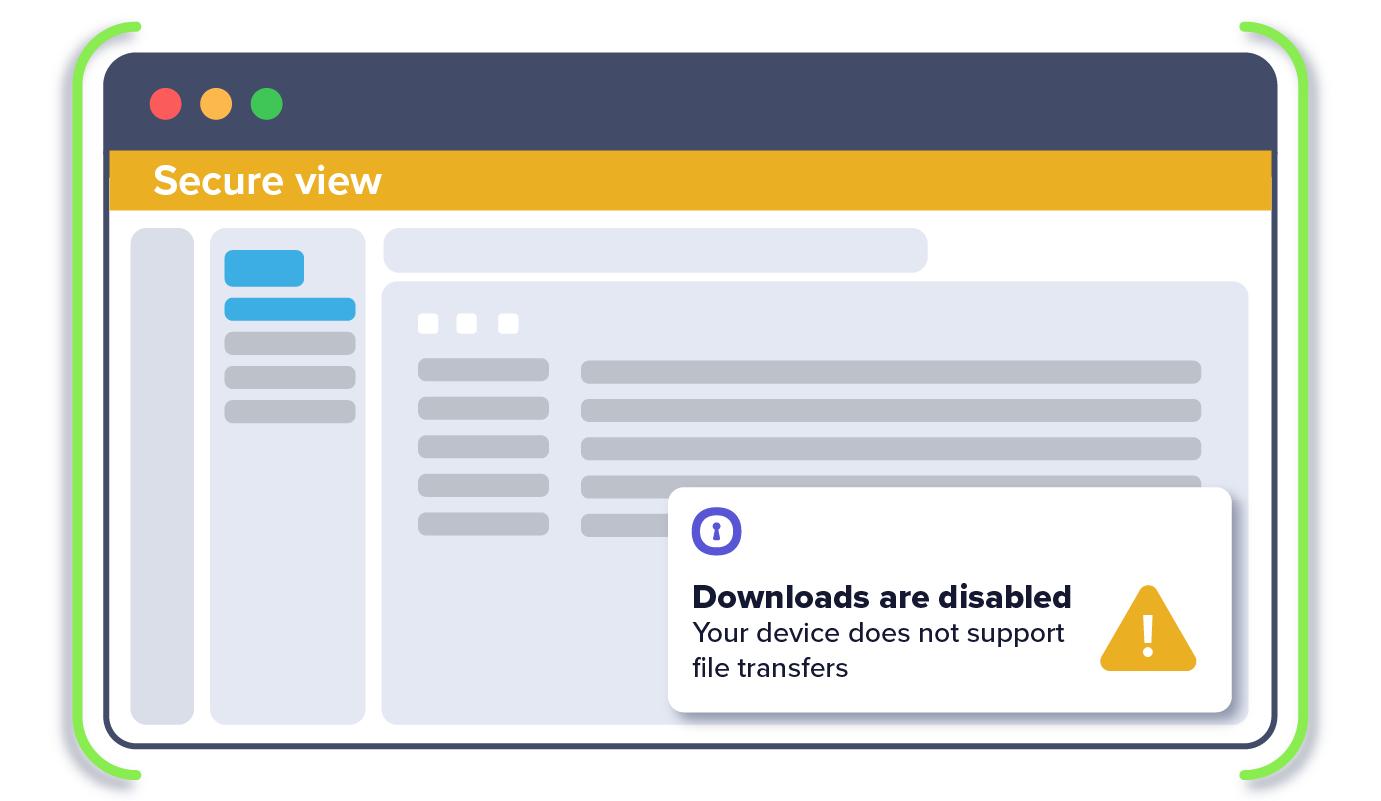
Enforce data policy controls across apps and websites to prevent leaks.
A zero-trust cloud browsing architecture purpose-built for the cloud.
Built on open-source Chromium — looks and behaves as expected.
Organization-wide visibility and control over web usage and data transfer actions.

1. IT sets data loss prevention (DLP) policies for data transfer actions that can be taken in the enterprise browser (e.g., copy/paste, up/download, print)
2. IT deploys Silo as the organization’s go-to browser, replacing the existing browser (e.g., Chrome, Edge) with a familiar, secure experience
3. All web-based activity — accessing apps, opening links, browsing for personal or business reasons — occur in a fully isolated, controlled environment
4. User’s data transfer actions (copy/paste, upload/download, print) are controlled in the enterprise browser