Employees request to visit dozens of websites every day on corporate devices. IT traditionally has been left with two ways to respond: block, or allow direct access, risking exposure to phishing and other link-based attacks, as well as accidental or improper user behavior.
With Risky Web Link Isolation from Silo, organizations now have a secure third option to allow access to untrusted websites and control what users can do with data while visiting.
Eliminate your attack surface exposed to malware while browsing.
Enforce data loss prevention policies for website categories or URLs.
Insert isolation and control where, when and how you want.
Seamless in-tab user experience — no software downloads required.
Easily add or delete users thanks to flexible capacity.
Gain all the benefits of a solution built in the cloud, for the cloud.

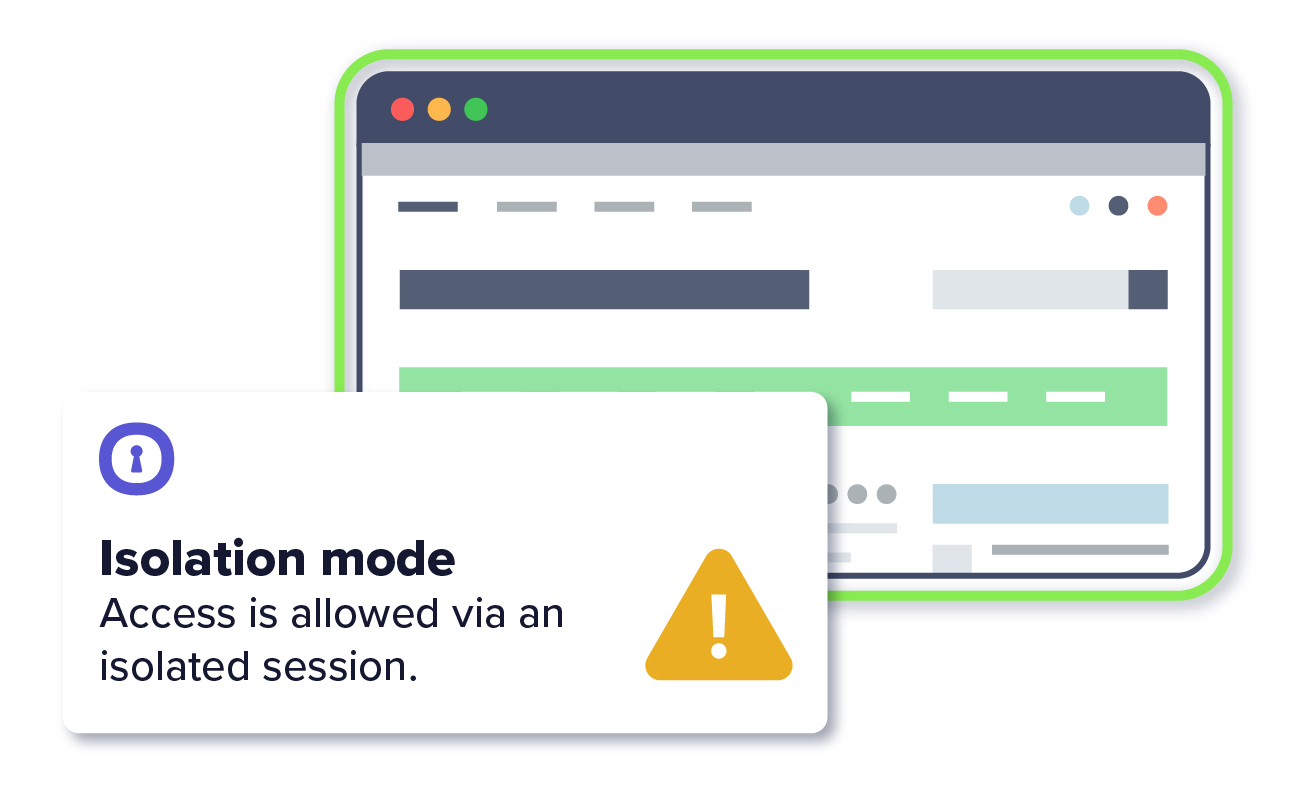
1. IT sets policies in their gateway for the categories or URLs to open in an isolated session
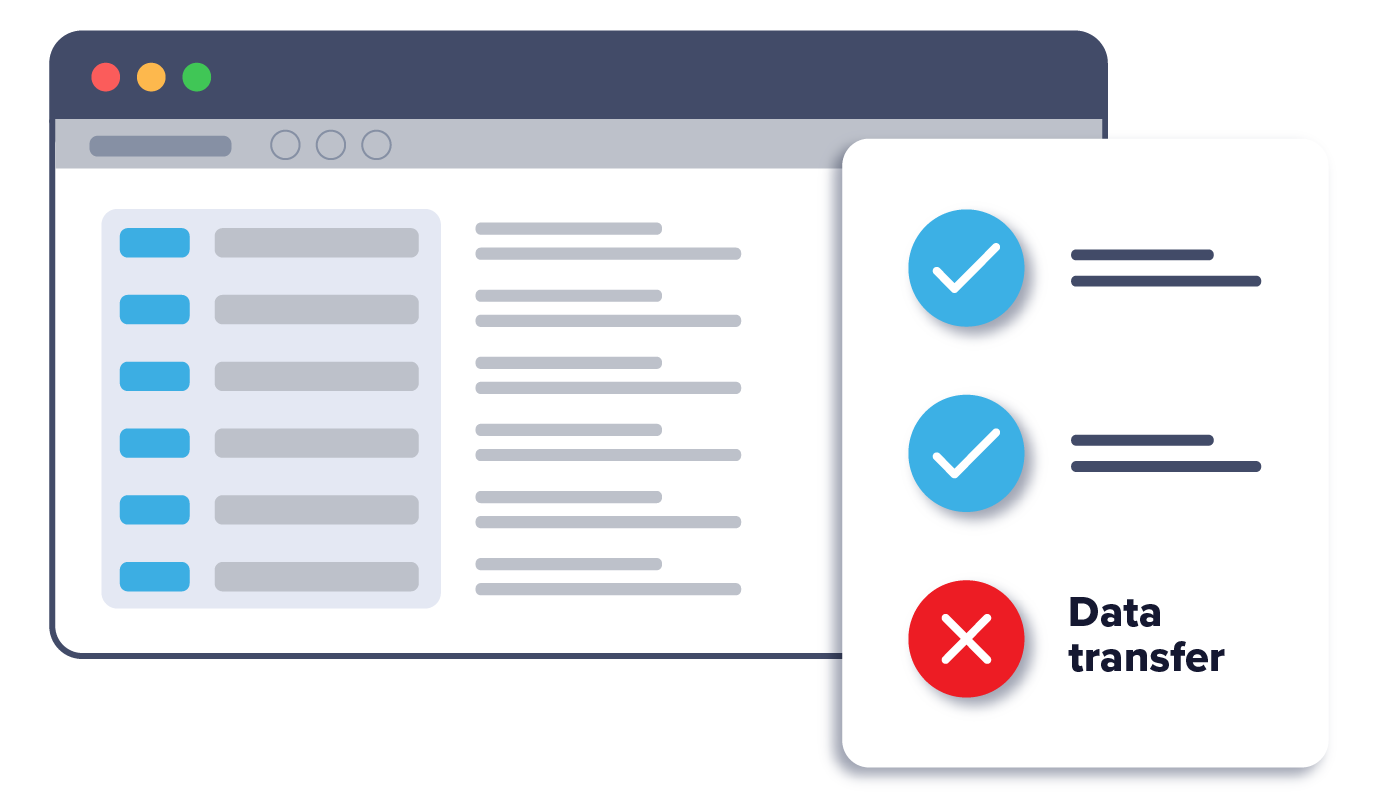
2. IT sets data loss prevention (DLP) policies
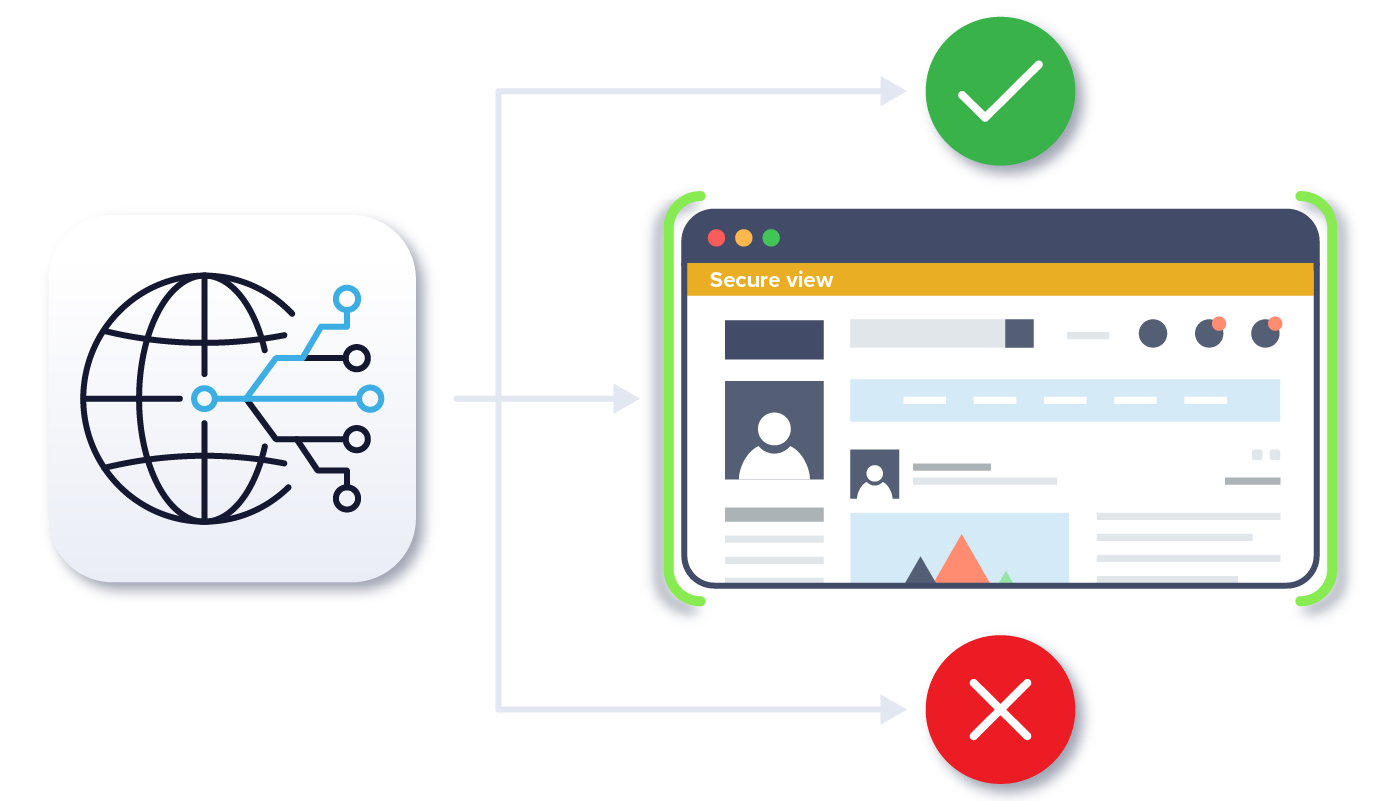
3. User’s URL request goes to the firewall or gateway where it’s determined if the page can be opened directly, blocked entirely or must be opened in isolation
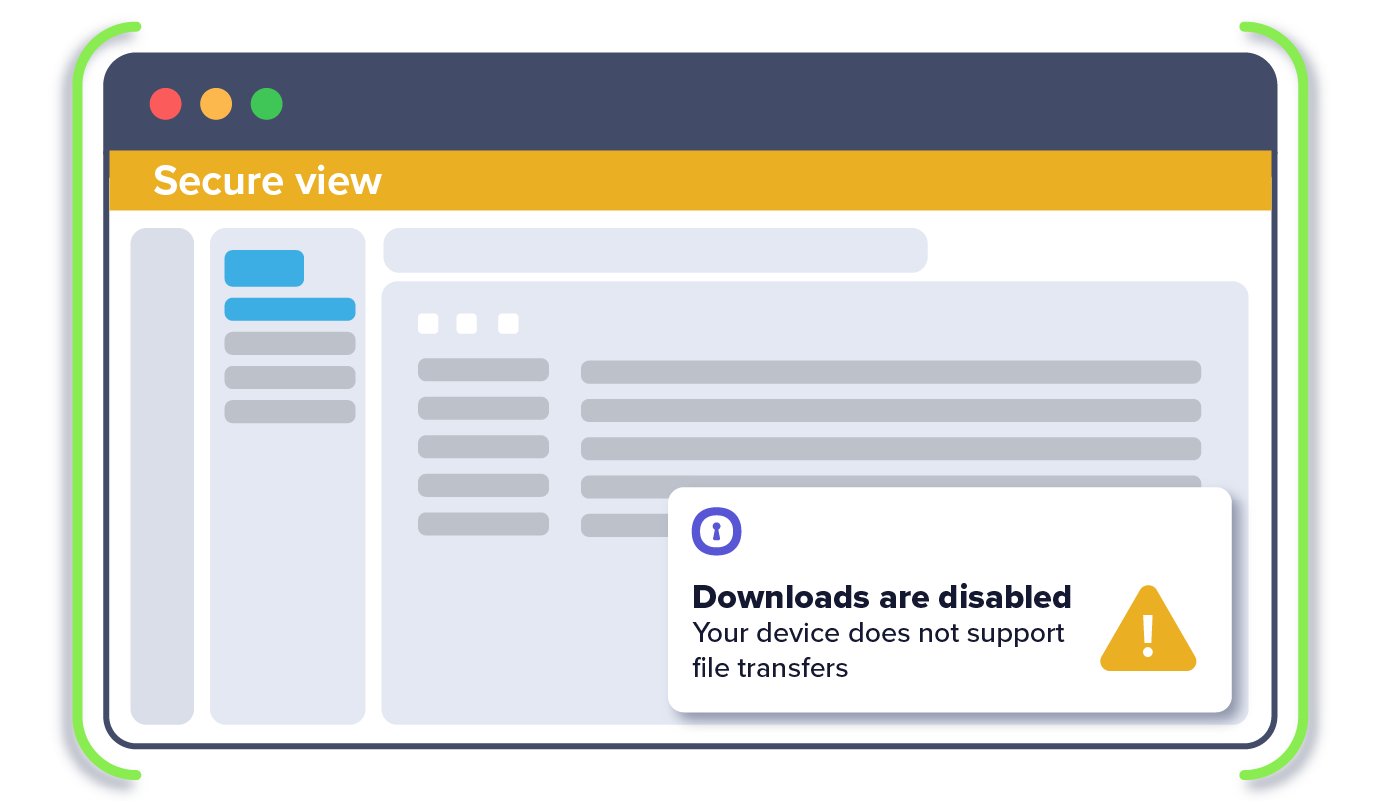
4. In isolated redirects, a new, fully isolated tab opens seamlessly in the existing browser (e.g., Chrome) — without user interaction
5. User’s data transfer actions (copy/paste, upload/download, print) are controlled in the isolated session