
Frameworks help you take a proactive approach to cybersecurity by giving you the information you need to track adversaries, understand their tactics, and take steps to prevent or respond to attacks. Leveraging these frameworks can lead to fewer incidents and improve focus on the biggest cyber risks, so organizations can pursue intelligence-building where it matters most.
Sabotage cyber adversaries
The Lockheed Martin Cybersecurity Kill Chain Framework defines the process by which attackers move through networks and identify vulnerabilities to exploit.
Use Case
The Kill Chain is a visual aid that helps investigators understand the steps adversaries must accomplish to compromise an organization — and where intervention can break the chain of compromise. While the free version is relatively bare bones, more detailed information is available in paid versions.
Stay one step ahead of cyberattackers
The MITRE ATT&CK Framework is a compilation of adversarial studies of TTPs based on more than 10 years of adversarial studies.
Use Case
ATT&CK has become the industry standard — and for good reason. Users can learn from long-term study of tactics and techniques of past adversarial attacks and how they differ between certain threat groups. ATT&CK also provides countermeasures to protect against specific adversarial behaviors, and can help organizations learn from attacks on similar entities to identify mitigation measures
Another way to use OSINT to proactively protect against threats is to leverage information sharing. Public forums can help you stay up to date on the latest trends, threats and malware, as well as improve your documentation of threat information and share current threat intelligence.
In addition to public forums, there are those that require paid membership, often specific to an industry, but still sharing open-source information — to those who pay their dues.
Data-sharing standard
The Structured Threat Information Expression (STIX™) is a language and serialization format used to exchange cyberthreat data. It uses JSON so that threats can be shared, stored and analyzed in a consistent way.
Use Case
The STIX format can help analysts improve their documentation of threats by using objects and descriptive relationships. This approach enables analysts to better prepare for and quickly respond to attacks because threat information is shared with structure and meaning. Note: requires a grasp of coding and engineering fundamentals.
How to exchange your CTI
The Trusted Automated Exchange of Intelligence Information (TAXII) is an open transport mechanism to share cyberthreat intelligence for STIX data via APIs over HTTPS. It is the preferred exchange protocol for STIX, but it can also transport non-STIX data.
Use Case
With STIX, CTI data can be shared with other researchers. TAXII users can share data with a specific trust group, share openly with many groups or require a request and response information exchange. Note: requires a grasp of coding and engineering fundamentals.
Find relationships and context
STIX Visualizer is a web-based tool that provides context about objects and relationships, converting blocks of JSON into a diagram with nodes and paths.
Use Case
Investigators get a visualization of threat information and see the relationships to other malicious links and files. The graphic depiction of CTI data lets users click on a node or path to further investigate. Note: Some threat intelligence platforms may have similar functionality built-in, but for those low on budget and with some coding/engineering savviness, the Visualizer is a great resource.
Better intelligence through community
abuse.ch helps to identify and track cyberthreats, focusing particularly on malware and botnets. The site operates multiple community platforms dedicated to a specific cyberthreat such as Malware Bazaar (malware samples), Threat Fox (IOCs) and URL Haus (URLs used for malware distribution).
Use Case
Users can browse abuse.ch databases to get information on malware, botnets, malicious SSLs, IOCs and YARA rules. Forums are also sharing information with threat intelligence platform and anti-virus solution vendors to improve services.

Time-to-insight is a key factor in proactive cybersecurity and cyber defense, so anywhere you can gain efficiency is important. Aggregators and APIs scour the web so you don’t have to — so efficient! These resources make searching the easier and faster, not to mention possible on the “unsearchable” dark web.
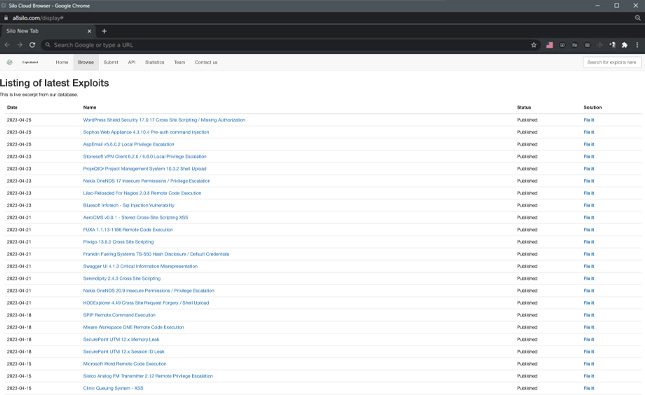
Evaluate your vulnerabilities quickly
The Exploit Database is a collection of public exploits and the corresponding vulnerable software. Exploits are curated from the internet and user submissions, then archived for community use.
Use Case
Researchers can use the exploit data (from exploits as well as proof-of-concepts) for penetration testing and vulnerability detection, making it a valuable resource for users who need actionable data.
Find and verify any business in the U.S.
The Secretary of State Business Search provides access to public information about corporations, limited liability companies and limited partnerships as filed with the state where they were incorporated.
Use Case
Enter the name of a business and a state, the search results display names of officers, date company was established, state of jurisdiction and more. The database is intended for banks and business lenders, but it is also applicable to CTI; for example, checking the validity of a business on a suspicious site.
Crack the code
Hashes is a website dedicated to hash recovery. Use this site to decrypt MD5, SHA1, MySQL, NTLM, SHA256 and SHA512 hashes.
Use Case
The Hashes site is useful when a hash value is found and needs to be tied back to the original value. For example, if a hash is found on Pastebin, pastebin-like or dark web site, the hash can be analyzed here for the clear text value.
Search the dark web
The OnionSearch (onionengine dot com) is a tool used to discover and aggregate dark web URLs from various onion search engines. Note: this is a surface website, but exercise caution when accessing from traditional browsers (e.g., Chrome, Safari). Using Tor to access this site is recommended.
Use Case
The Python script enables investigators to search a term through several dark web search engines at once, allowing you to efficiently find and extract .onion links matching the search term.
Get actionable data about remediation
The Cybersecurity and Infrastructure Security Agency (CISA) provides a catalog of known exploited vulnerabilities and the corresponding remedies.
Use Case
Users can sort by CVE, vendor, product and vulnerability name to search for exploits and get access to a catalog of exploited vulnerabilities to prioritize remediation efforts.
The tools category pertains to resources where you can input specific data points relevant to your investigation and get a result back. Use these resources to amplify your research, enable accurate pivots from known IOCs and further your investigation.
Some tools listed are open-source (i.e., publicly available code). While these tools are freely available, the downside is often that require a lot of “care and feeding” to use properly. On the flipside, having lots of eyes on the code can identify problems for continuous improvement.
Stay on top of exploits
ExploitAlert is a site that archives exploits and ways to address them. The site provides historical exploit data going back to 2005.
Use Case
Users search for exploits on the site and find available patches, mitigation measures, etc. Or users can integrate the API into their software to monitor exploits in real time.
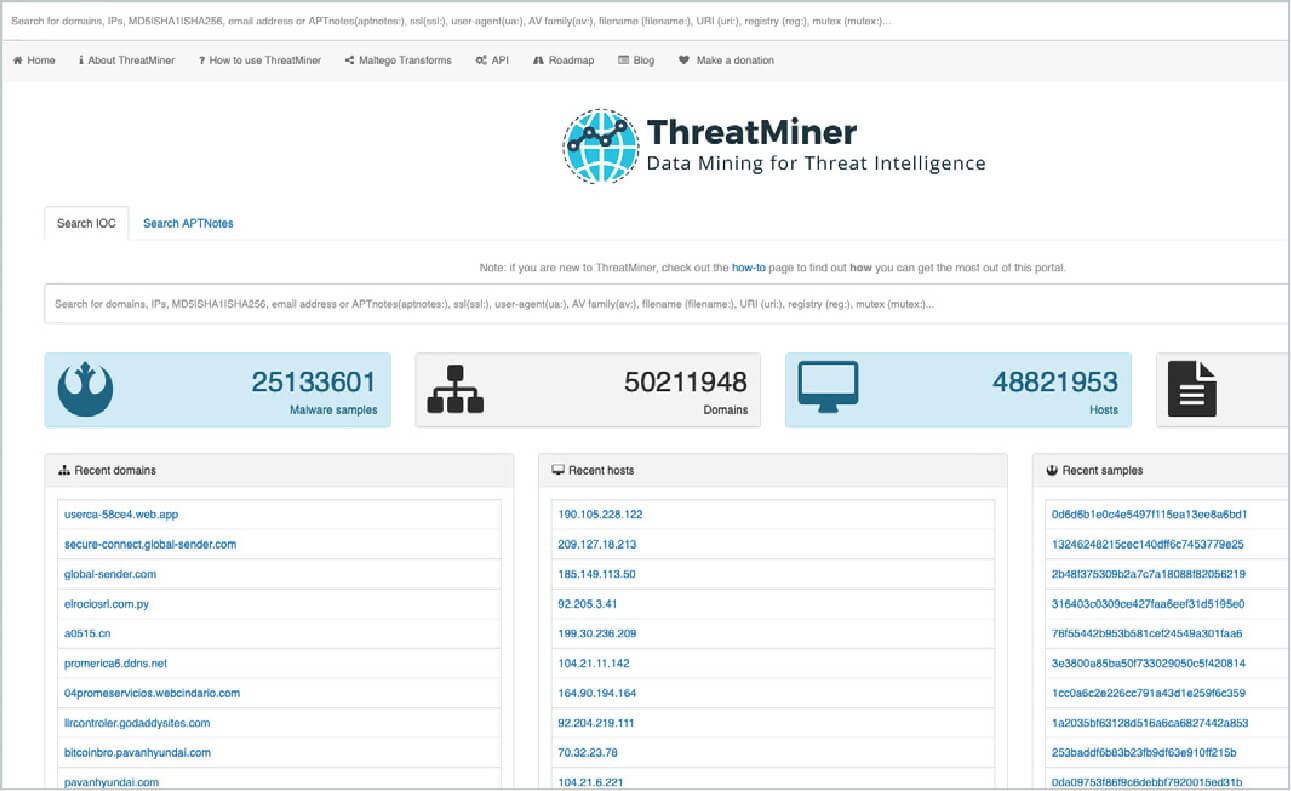
IOC lookup and contextualization
ThreatMiner is a threat intelligence portal designed to enable an analyst to research indicators of compromise (IOCs) under a single interface. That interface allows for not only looking up IOCs but also providing the analyst with contextual information. With this context, the IOC is not just a data point but a useful piece of information and potentially intelligence.
Use Case
Identify and enrich indicators of compromise to have a better understanding of attack origins.
Cut through the noise and eliminate false positives
GreyNoise Intelligence scours the internet for the IPs behind scan and attack traffic. During potential exploitation events, data from GreyNoise helps classify IP intent and accelerates alert triage.
Use Case
Researchers can use the API to integrate GreyNoise with common security products to look up IPs quickly and sift through security alerts. It also offers a visualizer to give the full context behind scanner IP addresses under investigation, including: JA3 and HASSH fingerprints, web path data, malicious/benign classifications, “spoofability,” behavior tags and ports and protocols scanned.
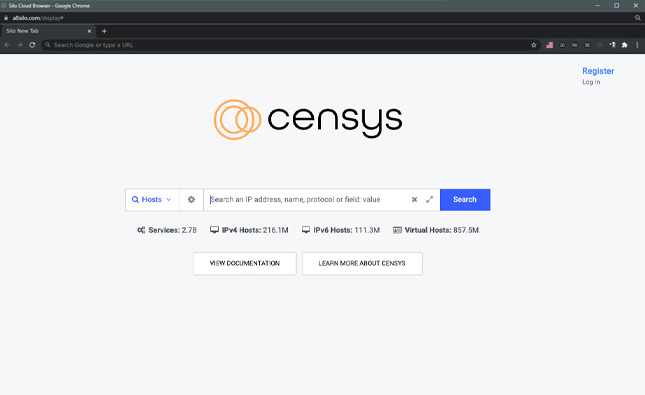
Identify exposures attackers can exploit
Censys is a platform that finds all devices connected to the internet (over 4 billion) and evaluates them every day, adding new IPs and removing old ones.
Use Case
Security professionals can query hosts and certificates through Censys’ web interface or API to identify exposures that attackers are likely to exploit. Censys also provides the historical information to know when an infrastructure was weaponized.
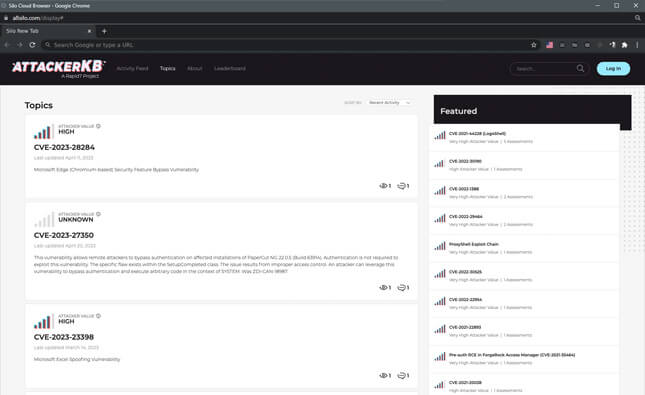
Focus your efforts with
AttackerKB is a web portal that crowdsources vulnerability assessments and threat details. Given the high volume of incoming vulnerabilities, this forum provides critical information so that defenders can triage threats and make informed decisions.
Use Case
Researchers get insights on which vulnerabilities they should address and mitigate, and which ones have a longer shelf life or are irrelevant to their business. AttackerKB shares real-time discussion about vulnerabilities that helps users cut through the chaos and noise of exploit alerts.
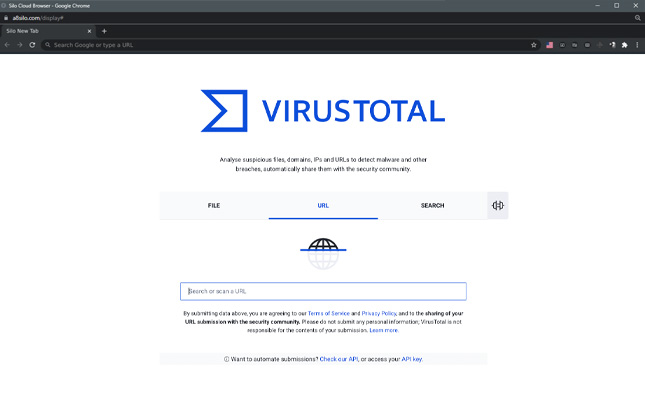
Analyze suspicious files and URLs
VirusTotal inspects items with over 70 antivirus scanners and URL/domain blacklisting services. Scanning reports produced by VirusTotal are shared with the public to raise the global IT security level and awareness about potentially harmful content.
Use Case
Users can select a file from their computer using their browser and send it to VirusTotal. Results are shared with the submitter, and also between the examining partners, who use this data to improve their own systems.
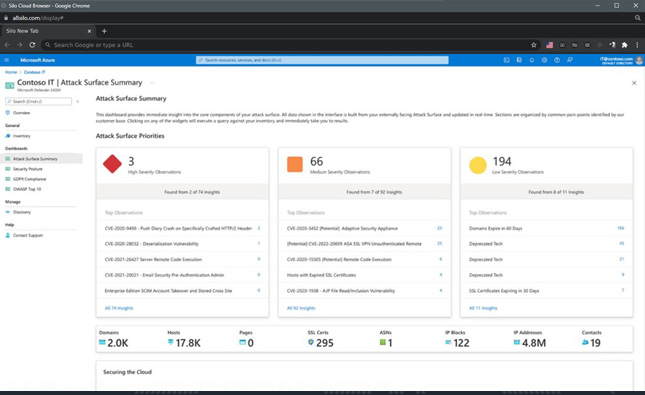
Uncover adversaries
Microsoft Defender Threat Intelligence (formerly RiskIQ) is a threat hunting and investigation platform that streamlines triage, incident response, vulnerability management and cyberthreat intelligence analyst workflows.
Use Case
Users can detect and respond to threats, prioritize incidents and proactively identify adversaries’ infrastructure associated with actor groups that can potentially target their organization.
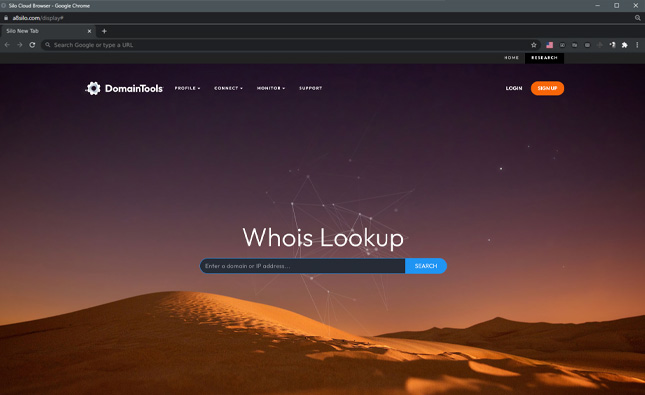
Get the details on any domain
DomainTools has tracked domain history since 1995 and makes it available to the public with an easy search tool.
Use Case
Using the “Whois Lookup,” researchers can enter a domain name or IP address and get information about the registrant, registrar, dates (created, updated, expires), name servers, IP location, IP history and more.
Find and lookup DNS records
DNSdumpster is a domain research tool that can discover hosts related to a domain. Finding visible hosts from the attackers’ perspective is an important part of the security assessment process.
Use Case
After a user enters a domain name, DNSdumpster identifies and displays all associated subdomains, helping map an organization’s entire attack surface based on DNS records.
The search engine for the IoT
Websites are just one part of the internet. Shodan allows analysts to discover which of their devices are connected to the internet, where they are located and who is using them.
Use Case
Shodan helps researchers monitor all devices within their network that are directly accessible from the Internet, and therefore vulnerable to attacks.
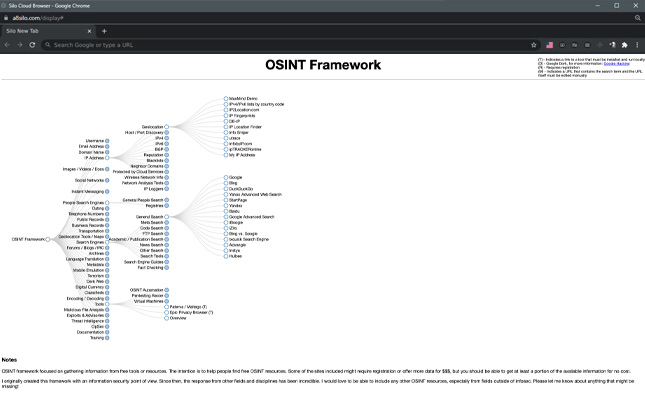
Find more OSINT resources
OSINT Framework indexes a multitude of connections to different URLs, recommending where to look next when conducting an investigation. It also provides suggestions on what services can help analysts find specific data that might aid in their research.
Use Case
When you plug a piece of data (such as an email address, phone number, name, etc.) into the framework, it returns all known online sources that contain information relevant to that data. The OSINT Framework also offers a list of potential resources where more information related to that particular source can be found.

Conducting OSINT research is a skill that requires regular practice to stay sharp. Online training courses are a flexible way to keep your skills current, make you more efficient and improve your cyber research.
Learn STIX at your own speed
The Cyber Threat Intelligence Training Center offers free, self-guided training, and provides information on the explanation and use of STIC/TAXII.
Use Case
Users can enjoy hassle-free, no frills online training for STIX/TAXII, intelligence analysis frameworks and integrating CTI into a SOC.
Share, listen, learn
The Cyber Social Hub gives investigators access to a professional network of cybersecurity practitioners.
Use Case
Connect, share insights, and collaborate with other CTI professionals. Plus, enjoy a variety of resources such as training videos, webinars, blogs, conferences and other events.