Proactive vs. reactive security defines how organizations defend against modern cyber threats: by either responding after incidents occur or preventing them before impact. By leveraging threat intelligence and secure environments to protect and mask investigations, teams can reduce risk, lower costs, and accelerate time to insight.
More organizations are shifting toward proactive security, focusing on anticipating and stopping threats before they impact systems or data. This approach relies on continuous threat intelligence integration to identify indicators of compromise (IoCs) earlier and reduce risk.
In this article, we will explain the difference between proactive and reactive, mention the different advantages of implementing a proactive security approach, discuss why operating in hostile environments is critical for proactive security defenders, and what the best tools are to achieve proactive security safely. However, before we start, let us discuss what the difference between a reactive and a proactive cybersecurity approach is.
The number of cyberthreats, along with their financial losses, is continuing to increase rapidly. For instance, the projected global annual costs of cybercrime are estimated to reach $23 trillion by 2027. Moving from a reactive to a proactive security posture greatly reduces both the frequency of successful attacks and the financial damage when breaches occur. According to a study conducted by Analysys Mason for a company with 200 employees over ten years, the following was found (see Figure 1):
|
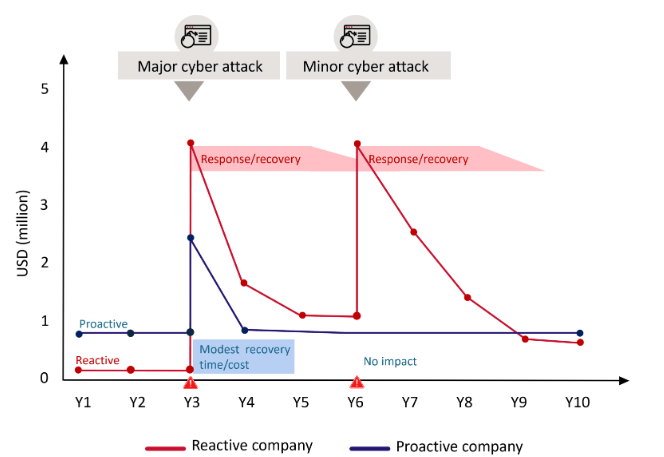
Figure 1 - Indicative direct cyber-security costs for a proactive and reactive business | Source: https://www.analysysmason.com/consulting/articles/cyber-security-approach
Reactive vs. proactive cybersecurity
Proactive vs. reactive cybersecurity defines how organizations defend against cyber threats:
- Reactive security is a response after an incident occurs
- Proactive security prevents, detects, and mitigates threats before impact
To have a mature and modern cybersecurity defense plan, you need to leverage both; however, the modern shift now is on proactive security because of its low costs and effectiveness compared to a reactive security approach.
There are different use cases of organizations using proactive and reactive security in their daily work. Here is a table that mentions some notable examples and the difference in how each approach responds to common security incidents:
Scenario | Reactive approach | Proactive approach |
Software flaw | Updating the system and patching it after a threat actor exploits a known bug to steal data | Run an automated vulnerability scanner weekly to discover security bugs and patch them before threat actors exploit them |
Employee error | Resetting the password of an employee's work account after clicking a phishing link | Conducting regular security awareness training programs and simulated phishing attacks to teach employees what to avoid clicking on |
Wide system access | Giving employee Admin rights on their account and revoking access when an account is hijacked | Use the least-privilege approach so employees can only access what is required to do their job and nothing else |
What are the advantages of implementing proactive security?
Proactive security is very important because it lends you more control over combatting complex cyberthreats. Adopting a proactive security approach provides numerous benefits to boost organizations' cyber defenses.
Prevents disruption to critical IT systems
By addressing security vulnerabilities in the IT environment before they are exploited by threat actors, proactive defense minimizes downtime and prevents disruption to critical business applications.
Lowers the need for reactive security measures
When threats are halted before they reach the organization's doors, then the need to handle security incidents is lowered dramatically. This helps minimize the resources needed to conduct incident response as it reduces the need to conduct investigations to a minimum.
Minimizes costs related to data breaches
When a data breach occurs, there are numerous costs associated with it, such as incident response, recovery, containment, and handling reputational loss. By having proactive security in place, these costs will be reduced.
Enables better responses to emerging threats
To execute a successful proactive security strategy, organizations need to employ continuous monitoring and invest in threat intelligence. This allows organizations to better respond to emerging and unknown threats.
Enhances stakeholder trust
Investing in proactive security will not only protect your organization from emerging threats but also increase its security posture against customers and other stakeholders, which helps, in turn, boost the organization's reputation and confidence in its ability to protect customers' private data and sustain its business operations.
Strengthens compliance with regulatory requirements
There are different regulatory requirements and privacy standards that either explicitly require or strongly imply a proactive security posture. For instance, the NIST Cybersecurity Framework (CSF) “Identify” function is inherently proactive because it focuses on knowing your assets, risks, business context, and dependencies before incidents occur.
Why is passive defense no longer sufficient?
Reactive security follows a deadly assumption that says you will know when you have been breached, and this is totally wrong. Today's attackers may remain for days within your network without drawing any attention.
For instance, the average dwell time (how long an attacker sits undetected inside a network) has historically ranged from weeks to months. But a recent study by Mandiant M (see Figure 2) estimates the dwell time to be 10 days for internally discovered intrusions and 11 days for external ones. This time allows attackers to conduct various malicious actions such as installing ransomware and stealing sensitive data from impacted organizations.
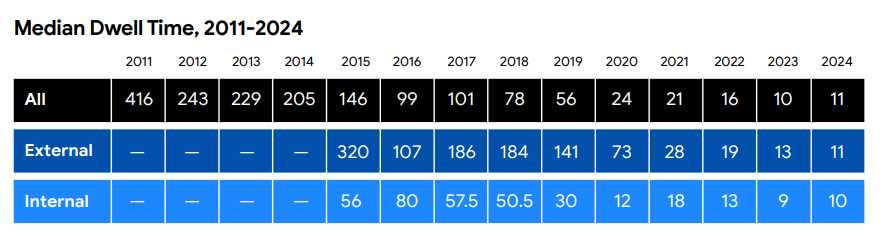
Figure 2 - Global median dwell time | Source: https://services.google.com/fh/files/misc/m-trends-2025-en.pdf
Passive defense tools such as firewalls, antivirus, and SIEM solutions are essentials for network security; however, they are not sufficient alone, because they are designed to detect specific signatures and attack patterns. Today's sophisticated threat actors, such as nation-state actors, organized crime groups and APT actors, are operating using normal network traffic and are using normal security tools that these security solutions cannot detect as malicious.
Why is operating in hostile environments critical for proactive security defenders?
Proactive security requires defenders to go where adversaries are to halt their operations before they cause damage or achieve their objectives. This entails collecting threat intelligence from the following disciplines.
Dark web and underground forums
Security teams need to access darknets like the TOR dark web, in addition to accessing darknet discussion forums such as BreachForums, and surfing Telegram channels and IRC networks to:
- Monitor the sales of the organization's stolen credentials
- Monitor chatters and negotiations between ransomware operators offering your organization data for sale
- Discover zero-day security vulnerabilities advertised for sale that impact your current software stack
- Monitor any mention of your organization in hacking boards, such as discussions to target your employees with phishing campaigns
Cyber threat hunting
In cyber threat hunting, the defenders assume hackers are already within their network, and they actively search for them using different methods and techniques. Hunters use the same attack techniques leveraged by threat actors and aim to discover anomalies before an alert is triggered.
Threat hunters leverage the following techniques in their work:
- Hypothesis-driven hunting (Intelligence-Led): For example, threat hunters built hypotheses from threat intelligence (e.g., mapping to MITRE ATT&CK techniques rather than building generic scenarios).
- Behavioral baselining: Establish normal baselines per host, user, and service account, so they can detect deviations, such as privileged actions outside normal time windows.
- Conduct endpoint device forensics: Inspect end devices for abnormal activities or artifacts, such as:
- Reflective DLL injection
- Unbacked processes
- Run keys in the Windows registry
- Scheduled tasks and services that reveal covert execution paths
- Data exfiltration detection: Looks for compression + encryption chains, such as creating archives in temp directories
Honeypots and honeynets
Deception technology involves deploying decoys inside your IT environment to gather intelligence about threat actors. For example, security teams can install fake servers, files, and entire network segments. When these fake entities are attacked, the attackers' tools, techniques and objectives are discovered by the defenders.
Red team operations
Red teams behave like adversaries; they use TTPs (Tactics, Techniques, and Procedures) documented in frameworks like MITRE ATT&CK to examine your defenses under realistic conditions. Red team operations require defenders to operate in a hostile environment that they have created to stress test their IT environment in real-world attack scenarios. This helps reveal blind spots before exploiting them by threat actors.
Active defense
Active defense is a term that refers to a set of proactive security actions that go beyond passive monitoring and focus on detection, disruption, and understanding of adversary actions, usually within a legal and organizational framework. Active defense is different from offensive actions in that it is usually limited to assets that you own, control, or are explicitly allowed to interact with.
Examples of active defense include:
- Intelligence sharing and law enforcement coordination: Working with various industry groups and law enforcement to report threat actor infrastructure, thus facilitating disruption and potential legal action against them.
- Infrastructure disruption via legal means: Initiating a domain or hosting takedown.
A good example of an active defense approach was that implemented by the Microsoft Digital Crimes Unit when they secured a court order to seize domains utilized by APT groups such as Fancy Bear/APT28 and the Necurs botnet. This involved proactive intelligence collection within hostile infrastructure to build the case for domain takedown.
What strategies and tools do organizations need to achieve a proactive cybersecurity posture?
In order to achieve a proactive cybersecurity posture, organizations need to move beyond just monitoring threats and start looking for threats from within and beyond their perimeters. This needs a combination of technology, intelligence, and a change in operational mindsets.
Managed attribution and isolated environments
The most important element in a proactive security approach is using isolated web browsing. When defenders conduct research on dark web forums or investigate phishing and malware infrastructure, they must conceal their digital identity and avoid exposing their organization's IT infrastructure to external threats.
For instance, a typical web browser will reveal the surfer's IP address, and digital fingerprinting will also reveal the investigator's computing devices and web browser characteristics, such as installed languages and fonts, display size, and location data. This information, while it looks trivial, allows tracking a user across the internet. In addition to revealing the investigator's identity, it will also alert the threat actor that they are under investigation.
| When operating in a hostile environment to gather intelligence, security teams should use a managed attribution service, such as Silo Workspace. This is a cloud-based web browser that allows them to change their IP address along with their digital fingerprint, while fully isolating the browsing session from the analyst’s local device and corporate network. Try it free for 30 days. |
Unlike other traditional approaches like using a VPN or virtual machines, managed attribution allows for granular control of how an investigator appears online, including aspects like operating system, browser type, language, time zone, and behavioral characteristics, so analysts can blend in with normal user traffic rather than stand out.
Continuous threat hunting
Instead of waiting for XDR, SIEM or other solutions to fire an alert, organizations should conduct continual threat hunting on their network. This is a proactive security measure that assumes a breach has already occurred and threat hunters are actively searching to find it.
There are different tools to conduct threat hunting and search within a large volume of threat data, such as EDR/XDR platforms (e.g., CrowdStrike, SentinelOne) and SIEMs with behavioral analytics (e.g., Splunk, Elastic Security).
Dark web and forum monitoring
Proactive security requires security teams to investigate the source of an attack before it happens. This includes searching within dark web discussion forums and other hacking boards for any indicators that point to the intent to attack their IT infrastructure. For example, a security team may discover their organization's employees' credentials are offered for sale on some darknet marketplace before they get exploited by threat actors to execute a ransomware attack.
Need to conduct digital investigations on the dark web? Check out The Professional Analyst’s Complete Guide to Investigating the Dark Web. |
A proactive cybersecurity posture is no longer optional. Organizations that fail to anticipate threats will always remain one step behind adversaries. By combining threat intelligence, continuous hunting, and controlled exposure to hostile environments, defenders can shift from reacting to incidents to preventing them, which ultimately helps reduce risk, cost, and operational disruption.
Proactive vs. reactive cybersecurity FAQs
What’s the difference between proactive and reactive security?
Proactive security focuses on preventing threats before they occur by using threat intelligence, continuous monitoring, and secure investigative environments.
Reactive security responds after an incident, prioritizing containment and recovery. While both are necessary, proactive security reduces risk, lowers costs, and enables faster detection of indicators of compromise (IoCs).
Why is proactive security important?
Proactive cybersecurity enables organizations to identify threats early, reduce dwell time, and prevent attacks before impact. By leveraging threat intelligence and secure investigation environments, teams can minimize financial losses, improve response speed, and maintain operational continuity in increasingly hostile digital environments.
What tools are used for proactive security?
Proactive security tools include threat intelligence platforms, EDR/XDR systems, SIEMs, dark web monitoring solutions, and secure browsing environments. These tools enable analysts to safely access, investigate, and respond to threats without exposing their identity or infrastructure.
How can I improve my organization’s security posture?
Improving your security posture requires shifting from reactive defenses to proactive strategies. This includes integrating threat intelligence, conducting continuous threat hunting, monitoring dark web activity, and using isolated environments to safely investigate threats. Platforms like Silo enable teams to protect infrastructure, mask identity, and accelerate investigations while maintaining compliance.
Tags Cybersecurity