Your browser knows a lot about you. If you want to stay truly anonymous online, you need to avoid being a unique snowflake and learn to control what information you share online.
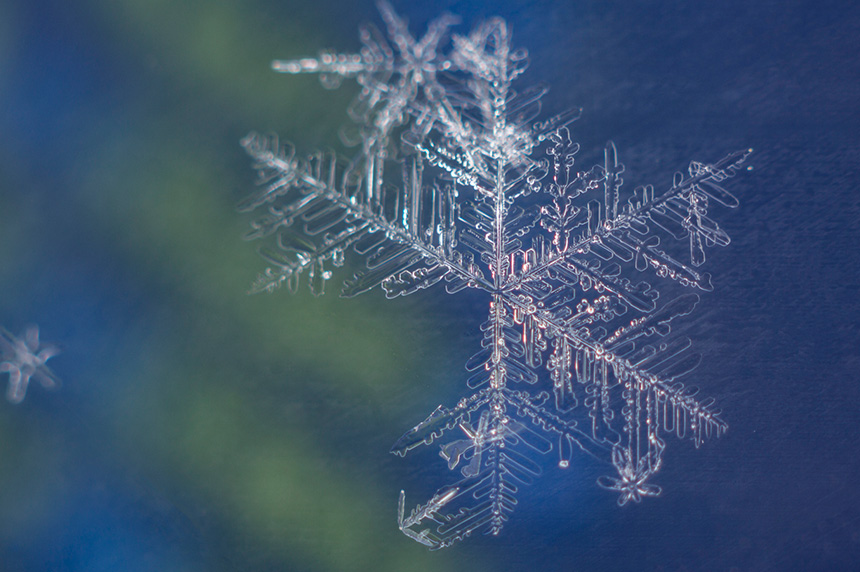
Commercial browsers such as Chrome, Firefox and Safari are designed to collect information about their users. They diligently track your online activity and catalog many seemingly innocuous details about your device, settings, location, language and more, to create your unique identity. These functions are designed to enhance the users’ browsing experience and tailor advertising content to their preferences, but for investigators, analysts and anyone conducting sensitive research online, these digital breadcrumbs can jeopardize their mission and threaten to expose their identity to a potential adversary or research target. Each identifier comes together like the crystal branches of a snowflake to identify a unique individual persona.
Understanding what type of information is being collected by the browser is key to creating a safe and anonymous browsing experience that helps researchers get work done without alerting their targets or even inviting retaliation — online or in the real world.
What’s in a digital fingerprint?
The most common thing that browsers track is cookies — bits of code designed to gather and save specific information about their users’ online sessions. But there is also a surprising amount of other data that websites and devices regularly gather to profile and even identify their visitors. While millions of web users around the world have similar devices and search for the same terms, websites are capable of fingerprinting specific visitors based on distinct combinations of settings and behaviors that make your online presence incredibly unique. Here are some of the common items that can help build your digital “profile”:
- Sites you visit and keywords you search for
- Your internet connection (IP address and provider)
- Type of hardware (device, OS, video and audio cards, etc.)
- Configurations and preferences (keyboard and language settings, time zones)
- Installed software and plugins
- Unique online behaviors (social media connections, shopping interests, websites visited, account activity)
- Battery status and other seemingly random things that help track you across browsing sessions
It’s not hard to find out what information is in your digital fingerprint. A quick assessment can reveal what an adversary may already know about you and your online behavior. Sites like AmIUnique.org can provide basic information about your online configuration and how trackable it is, as well as offer advice on how you can tweak it to blend in more easily. You can also get lots of helpful information on what type of data your browser is giving away on sites like Browserleaks.com.
For online investigators, blending in with the crowd is the safest way to avoid being detected. Sometimes in an effort to avoid detection, researchers incidentally make themselves stick out to webmasters. Unfortunately, simply turning off most commonly used cookies or switching to incognito or private browsing mode, does not offer a measurable degree of protection and anonymity. Every organization that relies on sensitive online research needs to design and build a comprehensive strategy for understanding what information is being tracked, and craft an approach on how to shield their analysts and protect their missions through blending in.
Learn more: What VPN and Incognito Mode still give away in your online identity
Managing your digital fingerprint
There are many ways to control how you appear online to the websites you visit, and manage what identifiable details they can collect about you. These details are commonly referred to as “attribution” and online researchers tend to employ a combination of various methods to try and disguise their online activity and intent.
Non-attribution: Some organizations prefer to equip their researchers with standalone devices that are not connected to the company’s network. While these systems help shield devices and networks from potential web-borne threats and don’t immediately reveal the user’s affiliation, they are often cumbersome and expensive to maintain and do little to help the user blend in with the usual traffic. Over time, even a clean machine begins to accumulate attribution, making the user vulnerable to tracking.
Misattribution: the intent of misattribution is to maintain a false identity online and disguise one’s location through the use of VPN, private browsing mode and other means. While effective in some cases, these methods still only partially obfuscate the user’s identity, and a well-funded adversary can still gather enough identifiable information about the researcher to reveal their intent.
Managed attribution: the most effective approach, managed attribution lets online researchers control and customize how their digital fingerprints appear to the sites they interact with online. It gives analysts the ability to manipulate any number of identifiable details, such as keyboard and language preferences, time zone selections, browser and OS settings, and more. By matching these details to typical visitors of sites they’re investigating, analysts and online researchers can blend in with the crowd and avoid tipping off their targets. A well-crafted managed attribution solution can help researchers customize their digital fingerprint to blend in with in-region traffic, view sites in local languages and even schedule data collections at times corresponding to local time zones.
Cloud-based browsing eliminates persistent tracking and maintains security
A cloud-based browser is a strong foundation of a secure and anonymous online research strategy. Purpose-built for supporting online investigations, a cloud browser executes all web code remotely, so it never reaches the endpoint, rendering instead a benign video display that users interact with. Using a cloud-based browser not only allows analysts to isolate their research activity from their device and network — protecting them from malicious content — it can also segregate browsing itself. Advanced cloud-based browsers can provide a fresh, non-attributed session every time they’re launched; and paired with managed attribution, can control persistent tracking within a session.
Cloud-based browsers can also support multiple sessions — with each executing its own virtual container and using different digital fingerprints at the same time. This can help investigators segregate and not cross-contaminate browsing sessions for different sites of interest, different projects and different purposes (i.e., personal browsing vs. browsing for investigative purposes). With cloud-based browsing, researchers can blend in with the crowd and shred their unique snowflake identity.
With so much information collected about your every move, it’s hard to remain anonymous online. For ordinary internet users all this tracking is annoying at best, but for online researchers, digital fingerprinting can impede their ability to do their work and compromise the integrity of their investigations. Knowing what’s being tracked and having the right toolset to conceal their identity and intent can help organizations of all types use the internet to gather data on specific sites, activities and individuals – to better understand the latest cyberthreats, protect brands and reputations, and even investigate illegal activity and bring criminals to justice.
To learn more about controlling your digital fingerprint and managing attribution in online investigations, visit our blog. Or request a demo of our purpose-built solution, Silo for Research, here.